
Turn Data Tagging Efforts into Enforceable Cloud Controls
imPAC ingests data tags and lets you build policies that continuously enforce the right controls on every asset containing PII, PCI, or other critical data.
Request a Demo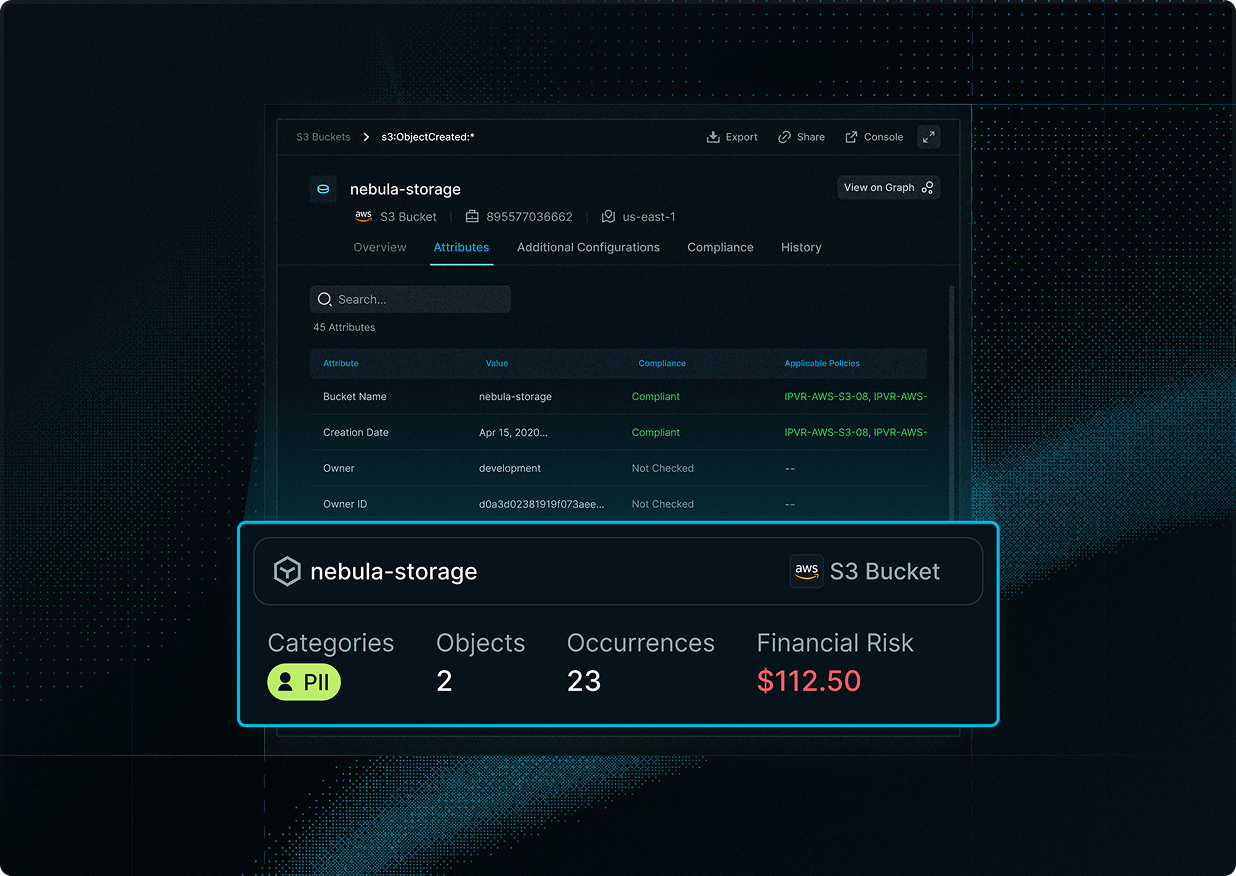
“imPAC bridges the gap between our data security tools and cloud controls, ensuring our most sensitive assets remain protected across all environments”
-CISO, Financial Services Company
Extend Data Protection to Cloud Infrastructure
Your tags tell you where sensitive data lives. But knowing an S3 bucket with PII is encrypted doesn't mean it's secure. imPAC extends your data classifications into holistic cloud controls:
- Ingest data classification tags and scope policies only to assets meeting specific criteria (e.g., storage accounts with over $100k worth of PII data)
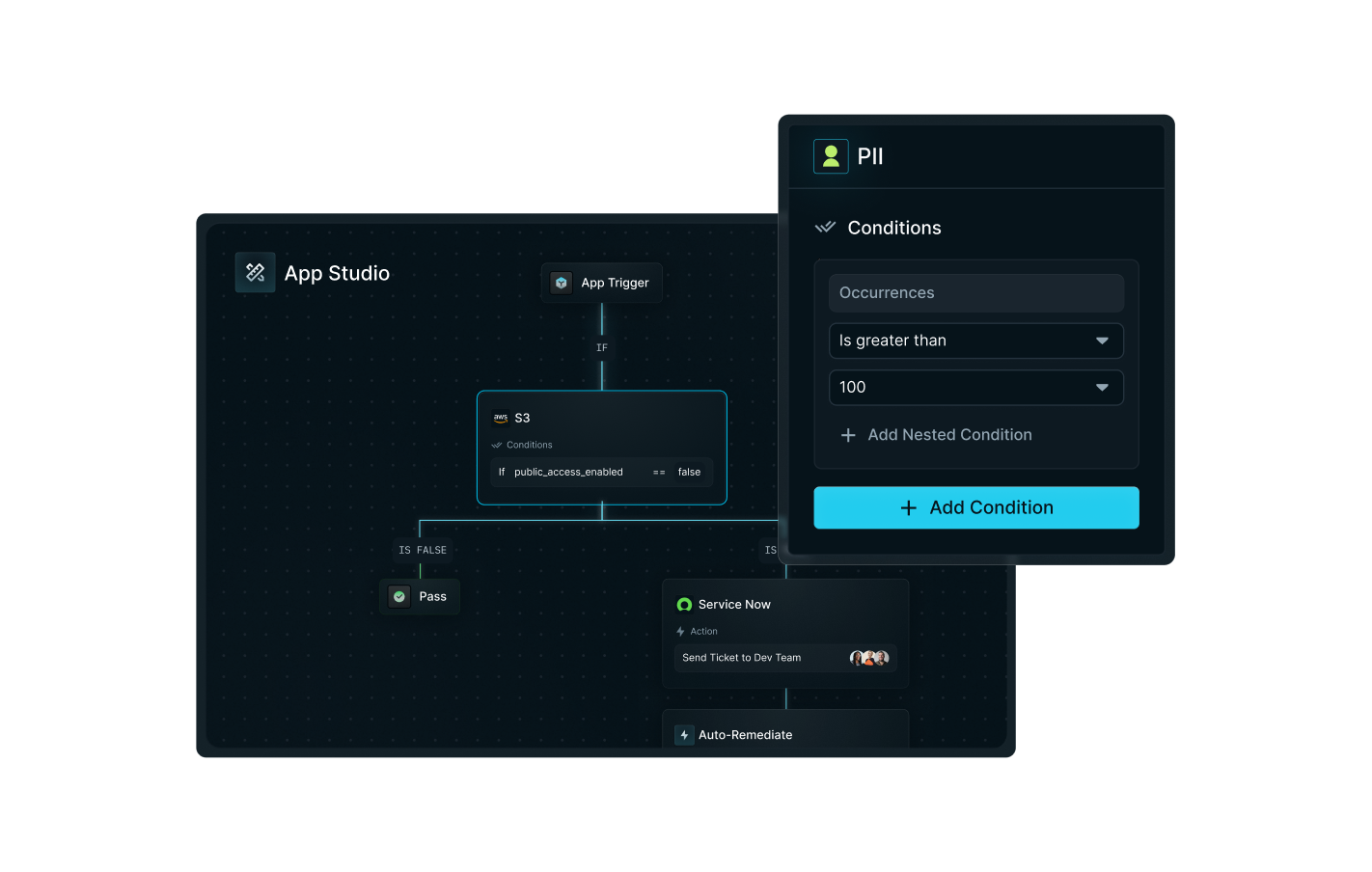
- Define required asset controls like replication rules, key rotation, resiliency measures, and residency rules in a single policy that can be applied across clouds
- Auto-generate remediation steps when tagged assets fall out of compliance and validate that fixes are implemented correctly
How It Works
Integrate imPAC with DSPM providers and build enforceable policies:
Integrate imPAC with DSPM providers like Cyera, Varonis, and BigID
Ingest data classification tags that are automatically mapped across imPAC's detailed asset inventory model
Build highly customized no-code policies that apply only to specific data types and requirements
Continuously monitor and alert when configurations drift and controls fail, keeping an auditable history
Business Impact
Operationalize DSPMs
Turn months of tagging work into actionable cloud policies at scale
Eliminate Noise
Scope policies to sensitive data to surface only relevant alerts
Know Critical Data Is Protected
Be confident that assets with sensitive data have proper controls in place
Real Answers
Show time-stamped evidence when execs or auditors ask "Is PII protected?"
Ready to Enforce Controls on Your Sensitive Data?
Request a Personalized Demo and see how imPAC secures your sensitive data across its entire lifecycle.